On a monthly basis I will publish my reading recommendations which mainly focus on Information Security (InfoSec) and Outdoor Sports. All InfoSec Reading Lists can be found here.
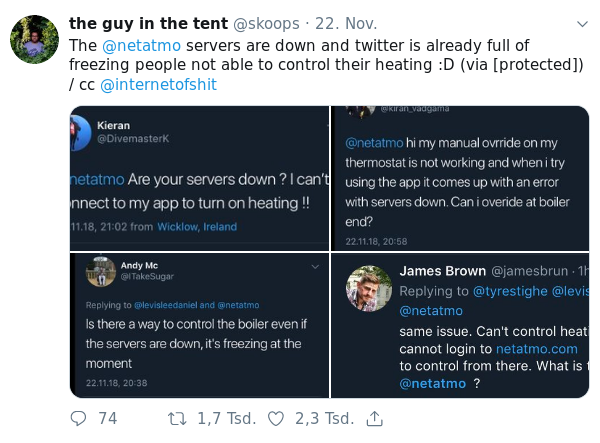
Quotes from the Twitterverse
InfoSec
- Zero-day RCE via XXE & SSRF on NetGear Stora, SeaGate Home, and Medion LifeCloud NAS - [link]
- How to Use DNS Analytics to Find the Compromised Domain in a Billion DNS Queries - “Finding a needle in a haystack is hard, but it’s nothing compared to finding a single piece of hay in the haystack that was put there with malicious intentions.” - [link]
- What the Marriott Breach Says About Security - Krebs regarding the latest Marriott Breach - “But anytime we see such a colossal intrusion go undetected for so long, the ultimate cause is usually a failure to adopt the most important principle in cybersecurity defense that applies to both corporations and consumers: Assume you are compromised.” - you can find my opinion regarding this principle here In case you follow the “assume breach principle”, the risk avoidance via deleting unnecessary data is a key step. As it seems, even US senators have heard that bell ringing: “We must pass laws that require data minimization, ensuring companies do not keep sensitive data that they no longer need.” - [link]
- Hiding Through a Maze of IoT Devices - hint: run port scans, close unnecessary ports even if you do not consider them as important (UPnP!) – scan again – repeat - [link]
- Facebook internal emails published by UK Parliament - [link]
- Locking Down Signal: A Guide for Journalists - “Even when your phone is locked with a password, anyone who picks it up can still read the message and sender name from your lock screen.” - probably one of the most common security failures - be aware that this could even include 2-factor-authentication tokens coming in via SMS - so lock your device properly or you are still at risk when your phone gets stolen even in case the adversary cannot access your phone / unlock the screen - [link]
- Which of the OWASP Top 10 Caused the World’s Biggest Data Breaches? - there are some pretty obvious results in this research which however are great to get confirmed: “Which OWASP Vulnerabilities are missing from the top 50 breaches? A3-XSS and A8-CSRF + A10-Unvalidated Redirects and Forwards” - [link]
- On Ghost Users and Messaging Backdoors - “What, exactly, is “responsible encryption”? Well, that’s a bit of a problem. Nobody on the government’s side of the debate has really been willing to get very specific about that.” - [link]
- Mondelez’s NotPetya cyber attack claim disputed by Zurich: Report - “He explains that the onus will be on Zurich to prove that the exclusion applies, but this could also be a difficult task given the information to prove where the NotPetya malware actually came from could be a guarded state secret.” – the outcome of this could be interesting and important for further cyber insurance cases - [link]