On a monthly basis I will publish my reading recommendations which mainly focus on Information Security (InfoSec) and Outdoor Sports. All InfoSec Reading Lists can be found here.
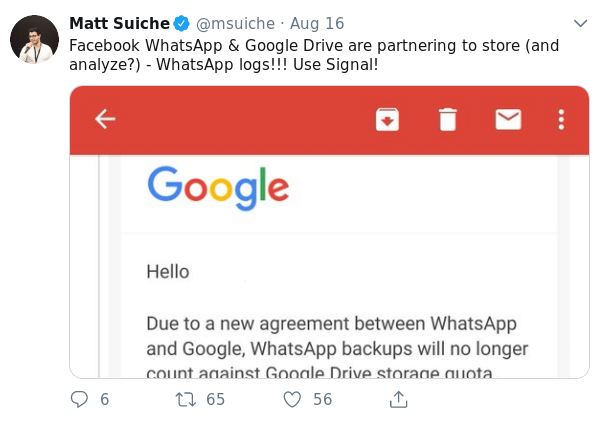
Quotes from the Twitterverse
InfoSec
- Who Wasn’t Responsible for Olympic Destroyer? - The threat actor responsible for the attack has purposefully included evidence to frustrate analysts and lead researchers to false attribution flags. - one of the reasons why attribution is so complicated and so dangerous - good article showing the possibilities you have as an investigator and the difficulties - Attribution is hard. Rarely do analysts reach the level of evidence that would lead to a conviction in a courtroom. - [link]
- How Apple store all your email metadata for years on their servers - [link]
- Why you need a better handle on the WhatsApp, Signal and Telegram apps - interesting perspective on the perception of people - Second, 50 percent of the study’s participants said they believed SMS text messages and landline phone calls were just as secure, or even more secure, than an encrypted message. - don’t blame the people, blame our industry which still does a bad job in terms of communication and awareness - [link]
- A Look Into Signal’s Encrypted Profiles - one of the reasons to choose Signal over WhatsApp - [link]
- Remote Code Execution on a Facebook server - [link]
- The dark side of XSS and hacking into Password Vault - no, not only used for pop-ups - [link]
- Smartphone security risk compared to “having a ghost user on your phone” - fresh research on Android ecosystem - Also shown in the video, and possibly more worrisome, is the ability of AT commands to bypass the lock screen - By sending one command, despite there being a password enabled, you could just skip straight to the home screen. It was quite shocking because this was all done with little text commands we were sending through a USB cable. - [link]
- View Private Instagram Photos - [link]
- Remote Mac Exploitation Via Custom URL Schemes - Applications can “advertise” that they handle various documents or file types - The OS will automatically register those “document handlers” as soon as the app hits the disk - a clever abuse of what was meant to make things easier for the enduser now ends up in a big threat called Windshift APT - [link]
- CLI: improved - [link]
- FakesApp: A Vulnerability in WhatsApp - [link]
Outdoor
- What Happens to Your Body When You Climb Everest - [link]